Extracting NSX DFW Rule Hit Counts
With the introduction of NSX-v 6.4.2, NSX will now log the firewall rule hit count for each firewall rule in the DFW. You can then check the UI or API for the hit count on each individual firewall rule. This capability is fantastic, however there is no way to extract the hit count for every rule in the environment either through the UI or API. Hopefully the API is updated in the future for this feature ;)
To get the rule hit count for all rules in the environment, we need to extract each of the firewall rule IDs and run the API command to get the hit count for each rule. We will then export this information in a CSV file and optionally email it to the requestor.
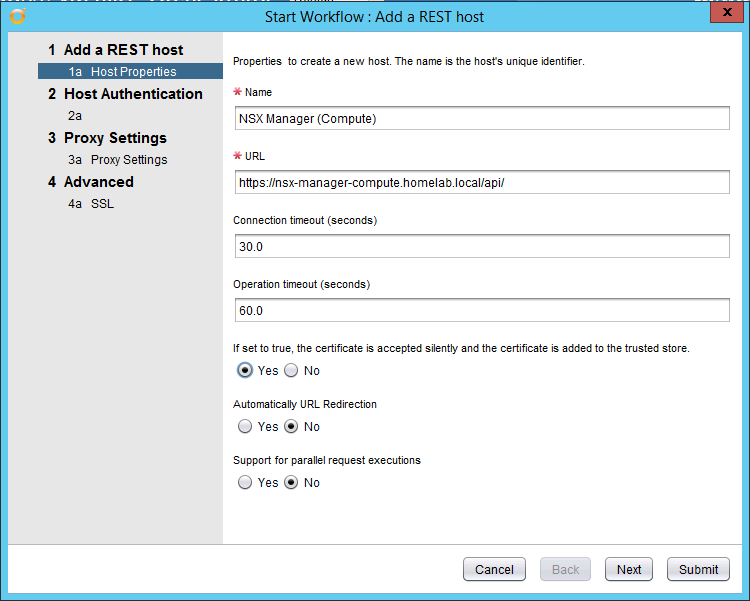
To begin, open vRO and create a HTTP-REST Host for each of your NSX Manager instances. Note the URL should be the FQDN with /api/ appended to the end.
Name: NSX Manager (Compute)
URL: https://nsx-manager-compute.homelab.local**/api/**
Silently accept the certificate: Yes
Host Authentication Type: Basic
Session Mode: Shared Session
Username: admin
Password: ****************
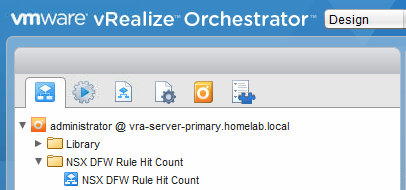
Once the REST Hosts have been added for each NSX Manager instance, import the workflow package org.nsx.dfwrulehitcount.package from GitHub or code.vmware.com to vRO and the workflow will be imported.
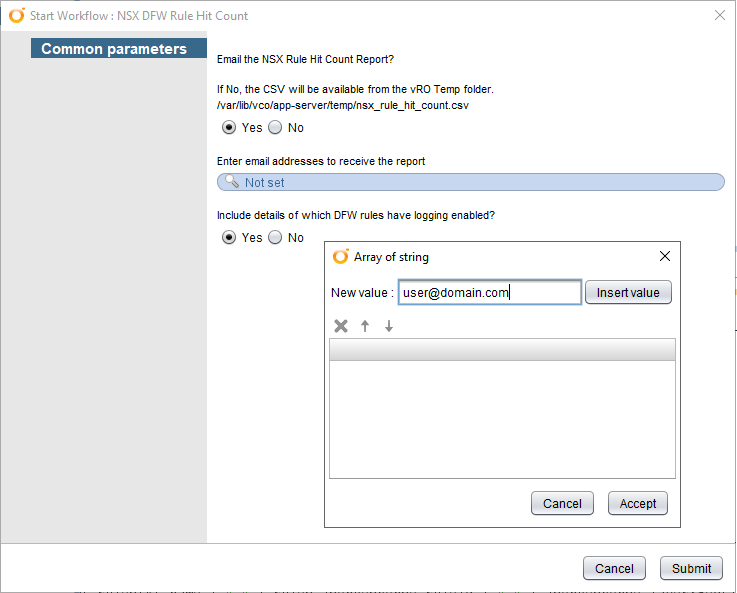
Before running the workflow, edit the workflow and adjust the email_xxxxxx attributes to suit your environment. You will need to enter a email_smtpHost, email_fromAddress etc. Once the attributes are set, run the workflow. You are prompted to select if you want to email the CSV and if so, enter the recipients email addresses, and then select Submit. This will run the workflow and email the CSV file to the email addresses provided if selected. If you selected no to emailing the CSV file, it can be accessed from the vRO Server at the location /var/lib/vco/app-server/temp/nsx_rule_hit_count.csv
Once you have the CSV results, this can be used to analyse the rules which are seldom hit and to optimize the firewall rule implementation.
Any suggestions on how to improve this or have a feature request? Please create an Issue on GitHub.
The output report will look like the below.